Is there finally a proper, thought-through strategy to deal with cybercrime? It seems that way. It hasn’t been formally announced, but was apparent from the details of this week’s world-wide bust of Labhost, a ‘one stop shop’ for phishing.
Very broadly speaking, the approach to cyber-crime has been to knock dodgy carding forums or dark net marketplaces off line. And ideally prosecute the administrators and key users – although that part has been extremely difficult, given most live in places beyond the reach of UK police.
I’ve been watching this for years. Criminal websites are taken offline, and the authorities celebrate a ‘big victory’. The sites then reappear under a new name a few weeks later, sometimes better than before. An expensive and disheartening game of whack-a-mole. But now the police appear to trying something new.
Like in most industries, cyber-criminals usually have a long-supply chain. No single actor can run an entire attack, and so will typically purchase or subscribe to various other services: buying stolen email addresses from a dark net site; using a text generator create believable messages; subscribing to a specialised platform to create believable fake websites; accessing a ‘bitcoin tumbler’ to launder any stolen money, and so on. Whether it’s phishing, ransomware, website spoofing – most criminals now pay others to do the hard technical work. This is known as ‘cyber-crime as a service’. Anyone can be a top-class hacker these days. You just pay someone else to do it.
Over the last couple of years, Labhost had become one of the world’s most popular, and best run, cyber-crime as a service sites. For a few hundred dollars a month, criminals could access software that helped them send phishing SMS messages to victims (known as ‘smishing’), direct them to one of thousands of fake bank or e-commerce sites, and even intercept their 2-factor authentication messages in real time. By early 2024, 2,000 or so users were paying a monthly subscription fee, targeting hundreds of thousands of victims around the world.
Payment options for Labhost
And, as is standard now for all cybercrime as a service products, they made handy how-to-guides. ‘Stay Safe and Good Spamming!’
Tutorial on how to use Labhost
This was all running smoothly until this week, when a co-ordinated police operation – led by the Met Police – took over Labhost and arrested a load of the top administrators.
Here’s the new bit. The police have realised that if you dent criminal confidence in the tools they use, you increase their cost of doing business. They have to take more precautions, and might even decide it’s too risky. That in turn will reduce the number of people getting targeted. So rather than simply shut Labhost down and make generic statements about hunting down perps, the police made stylish personalised video messages for each and every subscriber, which outlined in detail their use of the site. Here’s one of the videos, and it’s worth watching.
“Welcome to your Labhost wrapped. Your recap of all the data we have about you. This recap has been made in partnership with international iaw enforcement”. The underlying message is this: you should never have trusted Labhost. Their security was poor. They kept all your IP addresses. And now we have them. You didn’t think any of this was really anonymous, did you?! The purpose is to freak these criminals out – to make them uncertain and wary of these ‘cyber-crime as a service’ products.
This is smart digital policing. Yes, I’m a little frustrated it’s taken so long. For some years I have argued that the key to the dark net markets is the use of customer reviews to create trust between. If you wanted to undermine that, the obvious way would be to flood the site with fake reviews. Better late than never though. And (you probably don’t hear this very often) the UK police are actually getting quite good at it.
This new approach really started earlier this year with Operation Cronos. Cronos took down Lockbit, which for the past few years was the biggest provider of ‘ransomware as a service’. (In case you don’t know – ransomware locks your computer files and criminals demand a hefty ransom payment in cryptocurrency to retrieve them. I wrote about that here too).
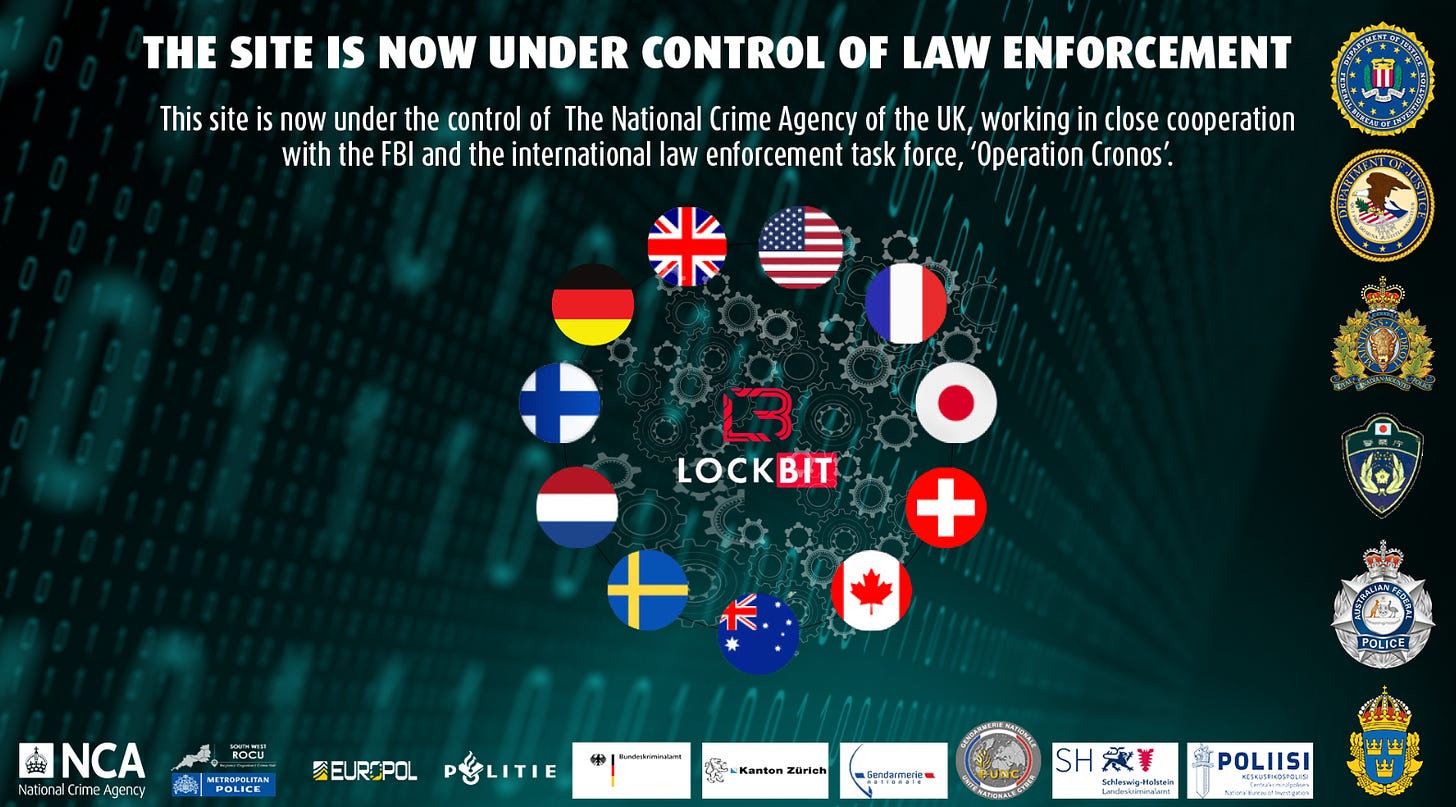
On the evening of February 19th 2024, Lockbit was taken over by the UK’s National Crime Agency.
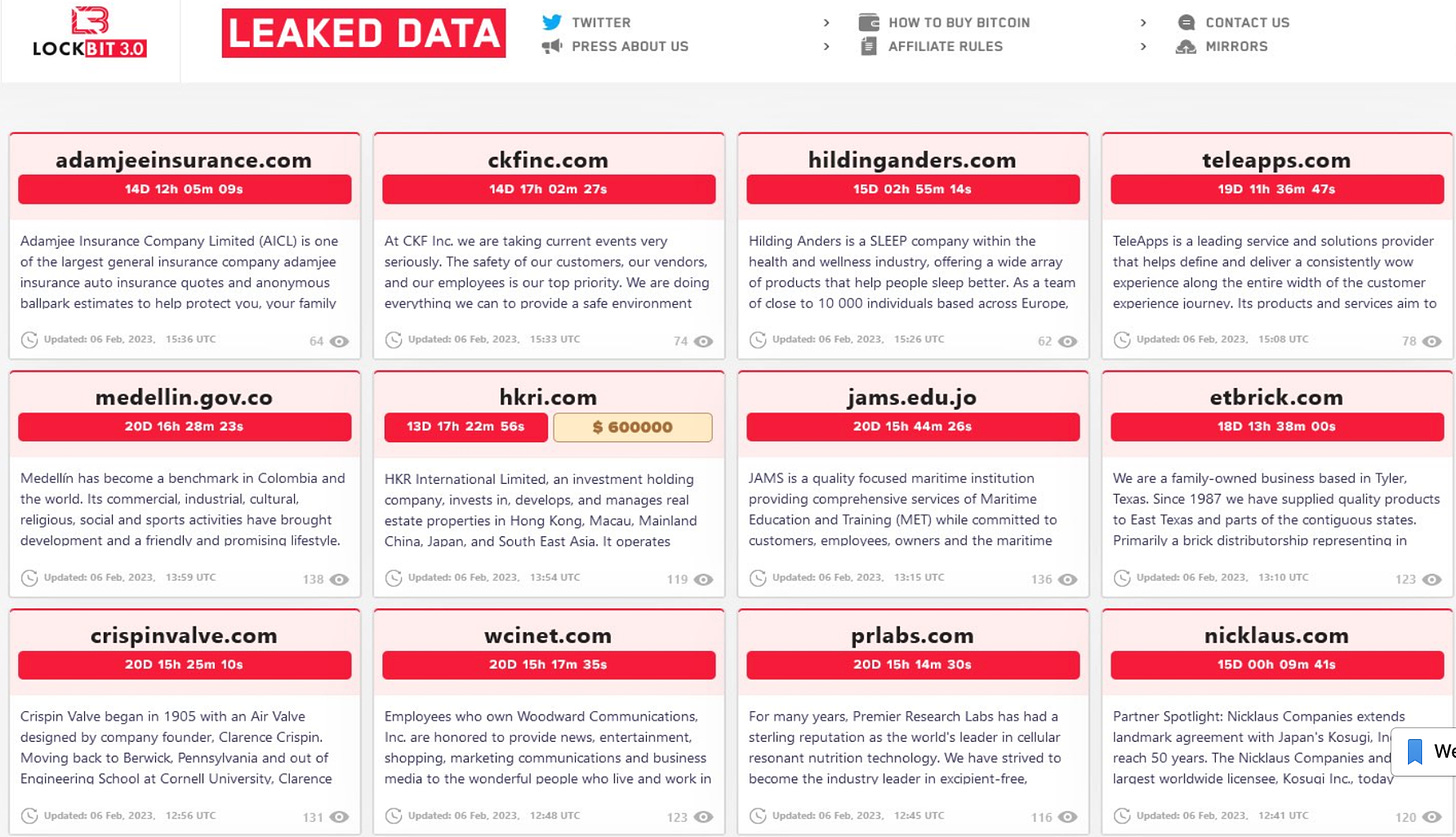
This time, they replicated the exact design of the Lockbit landing page, which was an evolving list of victims being extorted with a countdown clock. See below:
Lockbit: before it was taken over by the UK’s National Crime Agency
On 20th February, though, any Lockbit visitors found victims’ names had been replaced with press releases and information about the successful police operation. That’s actually quite funny!
Lockbit, after it was taken over by the National Crime Agency
The language the police used in their message to Lockbit criminals also pointed to this focus on spreading distrust and uncertainty: “You can thank Lockbit and their flawed infrastructure for this situation. You may be hearing from us very soon… have a nice day.” It was even little lulzy. I’d guess written by a former criminal hacker who now works for the police. On the underground forums, some even applauded how well the police had played their hand.
It’s still early days – and Lockbit is already back, albeit at a much reduced rate. But it seems to have the crooks shaken up, which is the whole point. Trendsmicro analysed the criminal chatter post-Cronos: “Disrupting and undermining the business model seem to have had a far more cumulative effect than executing a technical takedown.”
For years the battle against cybercrime has felt a little directionless. You take out one site, and a clone turns up five minutes later. The problem just keeps getting worse – as cybercrime gets ever easier to do. Whisper it, but it looks like we’re finally developing some smart techniques in this endless game of cat-and-mouse. Tom is getting smarter at last. And Jerry knows it.